Preventative Security Model™ Enforces Zero Trust Principles
As enterprise workloads increasingly shift away from the endpoint to desktop as a service (DaaS), software as a service (SaaS) applications, secure browsers, or virtual desktop infrastructure (VDI), the era of monitor, detect, and remediate is falling short to prevent ransomware and persistent cyberattacks on the endpoint.
The Preventative Security Model™ provides the framework to unify a modern endpoint strategy. IGEL reduces the attack surface by 95% by removing the endpoint vulnerabilities that are frequently exploited by bad actors. This prevents endpoint ransomware, dramatically reduces the risk of software update outages, and consequent disruption to business operations.
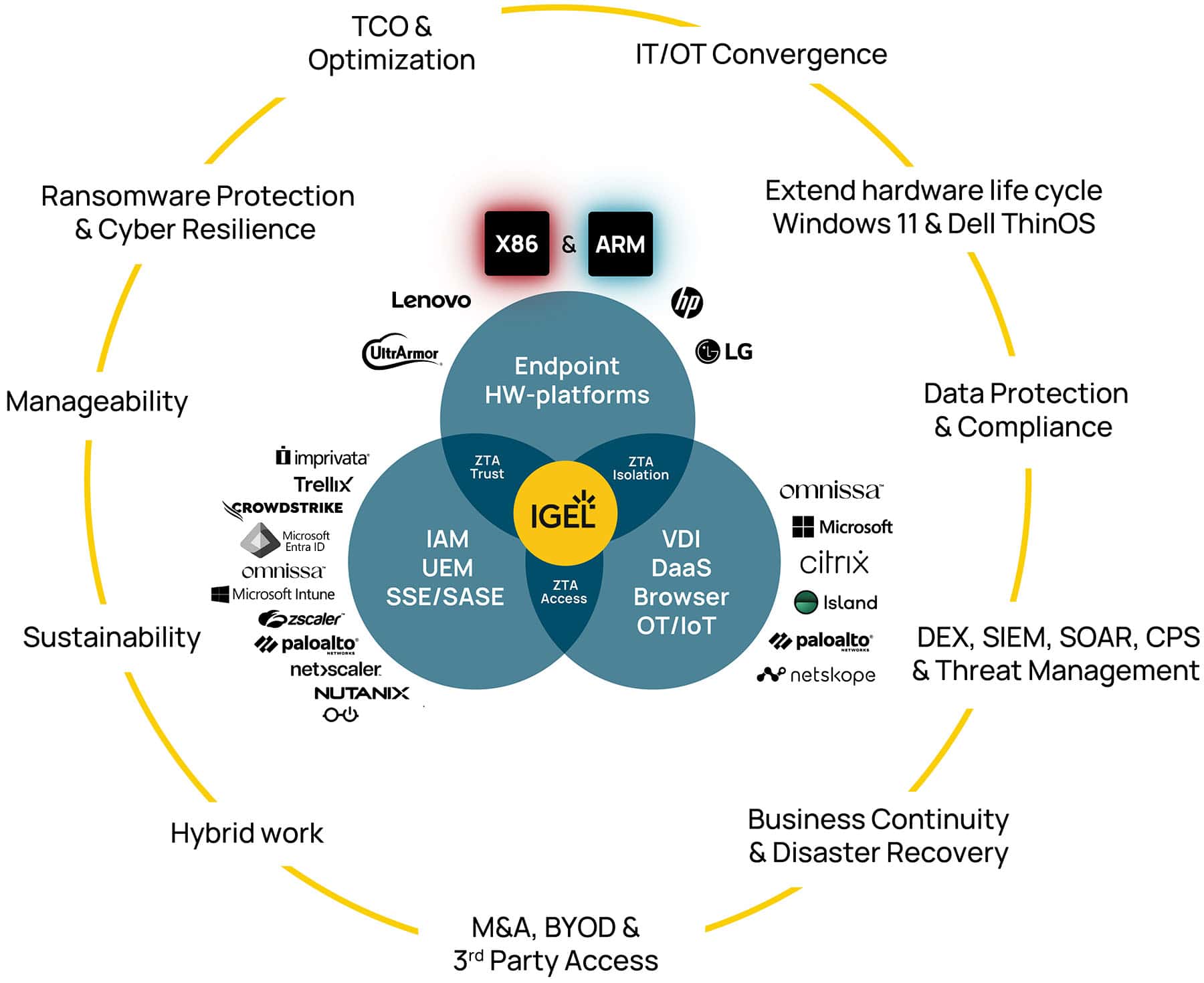
Utilized by many of the world’s leading healthcare, finance, manufacturing, retail and government organizations, IGEL supports key pillars of the Zero Trust architecture. At the intersection of hardware, applications, and security, the Preventative Security Model (PSM) establishes trust, isolates and enables smart login through integration with leading solutions in Identity Access Management, Unified Endpoint Management, Secure Access Service Edge. IGEL is pre-loaded on PCs, laptops, and thin clients from partners HP, Lenovo, and LG. The IGEL Ready ecosystem of validated integrations powers the PSM, so you can build your preventative endpoint strategy that scales with your policies and compliance mandates.
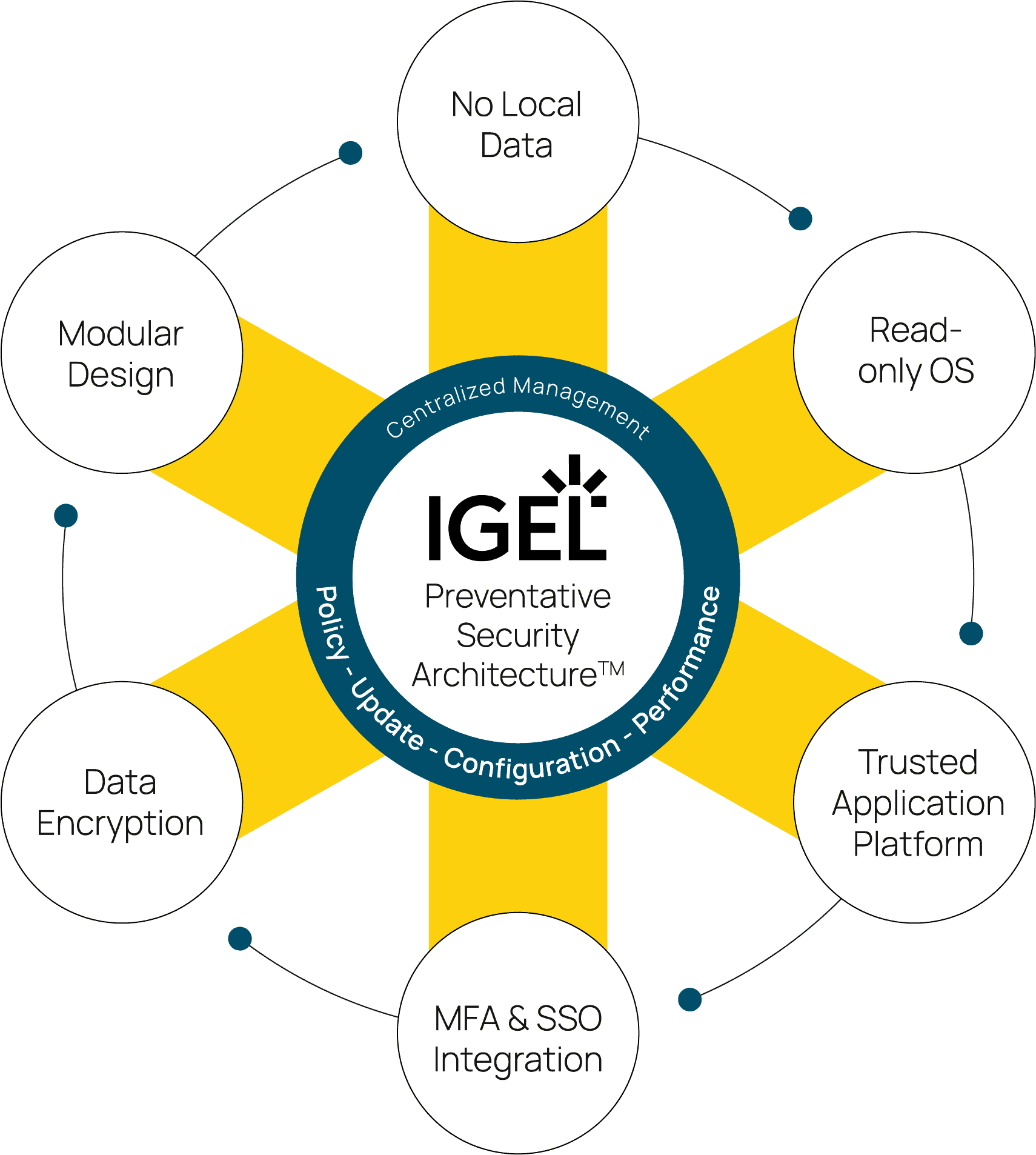
IGEL Preventative Security Architecture™
The Preventative Security Architecture™ underpins the PSM, is secure by design, eliminating risk factors at every layer of the endpoint experience.
Zero Trust at the Edge
The IGEL approach is transforming the endpoint to a proactive participant in Zero Trust security strategies. Once the most vulnerable and passive points on the network, IGEL has redefined the role of the endpoint with the Preventative Security Model. The IGEL OS platform embeds security into the endpoint itself, ensuring that trust is evaluated, and access decisions are informed by real-time context and dynamic configurations.

No Local Data Storage
No data exists on the endpoint. This could be in the form of a downloaded file, screen shots or cached files. IGEL OS does not permit users to store data locally, there is nothing on the device to exfiltrate. With IGEL OS on the endpoint, breach investigations due to a lost or stolen device can be immediately concluded.


Secure Boot and Trusted Application Platform
Each stage of the IGEL OS boot process is checked through a cryptographic signature of the next, starting with a UEFI secure boot and TPM on the hardware. This chain of trust ensures the integrity of the endpoint OS and enables a fast recovery from attempted cyber-attacks.
Shrink the Attack Surface
IGEL OS is a much smaller core footprint and attack surface than a traditional endpoint OS. IGEL OS 12 only contains what the user needs to accomplish their tasks. Additional functionality such as partner integrations with Microsoft, Omnissa, Island, security, IAM and UEM solutions are available on the IGEL App Portal and centrally provisioned through the IGEL Universal Management Suite.


One Workspace, Every User – The Power of the Adaptive Secure Desktop™
IGEL’s role-based, context-aware workspace delivery model adapts to meet the needs of every user, while enforcing the principles of failsafe security with the Preventative Security Model, orchestrated from a single platform with the Universal Management Suite.